WordPress is the most successful CMS platform so it’s no surprise that it will be the target of many hacking attempts. Because many small business owners are using WordPress, this potentially leaves them vulnerable to all the hackers trying to exploit their sites.
The basic WordPress installation is very secure against hacking, the majority of the problem lies when vulnerable themes and plugins are added. Criminal hackers rely on WordPress’ popularity and its large plugins and additional themes to inflict their damage.
Why Did Your WordPress Site Get Hacked
There are a number of ways that a hacker can take advantage of a site to install malicious content. Here are the most common:
- The theme you installed was already hacked
- A plugin or theme that was installed had an exploit (and was not updated)
- A hacker obtained access to your WordPress password
- A hacker had access to your Control Panel (web hosting) password
- A hacker infiltrated the web hosting files
The majority of small business owners will not be taking a chance at installing themes or plugins that come they find on the internet, but plenty of people do. Instead of paying for a theme from a developer, they will seek out sources on the web to find that same theme for free. Unfortunately, these themes and plugins are often times purposely altered so that they can hacked into at a later date.
A hacker can also use various phishing tactics to gather passwords to be able to log into your sensitive accounts, including your WordPress administration area to install whatever it is that they want. But by far, the most common way that a WordPress site is hacked is by not updating the theme and plugins files.
Four in Five Hacked Websites Are Running WordPress
Security firm Sucuri released its Website Hacked Report, in which it compiled statistics from over 11,485 compromised sites it was called upon to investigate over the past year.
Results showed that almost 80% all of hacked sites are built on the WordPress CMS.
The majority of hacks originated with third party installation of software to their site.
Point of entry for most hacks was a vulnerable plugin, not the CMS core
As for a breakdown of hacked WordPress sites, Sucuri says that a large part can be attributed to outdated plugins. There were minimal attempts to use vulnerabilities within core WordPress files itself.
“Three plugins are responsible for a quarter of WordPress hacking incidents”
Sucuri says that, from all the compromised WordPress sites they analyzed, they often found the intrusion point within a vulnerable plugin. A quarter of these attacks can be attributed to three plugins: RevSlider, GravityForms, and TimThumb.
Updating Your Plugins
The lesson here is that it is extremely important to keep your themes and plugins up to date. Failing to do so can leave you vulnerable if an exploit is found. Some hosting services will automatically apply updates to WordPress, but many do not, and most do not update the plugins at all.
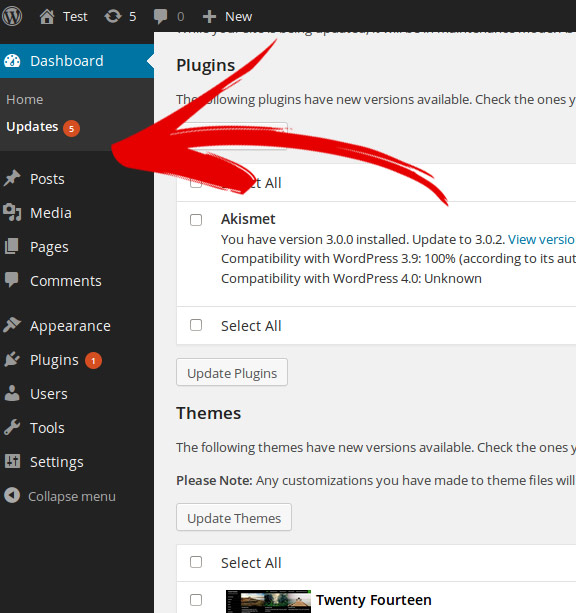
WordPress makes it easy to update plugins. There will be a very visible circle telling you the numbers items that need to be dealt with.
Wordpress Theme Timebombs
Another issue is that some WordPress theme developers choose to embed a plugin directly within the code of the theme. This allows them to make a more fully functional and integrated theme with many options and ‘cool effects’ that can be managed from a central theme control panel.
This is what happened in many cases with RevSlider, where many theme makers embedded it into a large variety of themes that people then used for their WordPress sites. In most cases, these were legitimate copies of themes bought from developers.
However, since the plugin was hard coded into the theme and not added in the usual WordPress plugin section, RevSlider could not be updated as a normal plugin. Unfortunately in cases like this, two steps have to happen to keep the site safe. The developer needs to issue an update to the theme with the new hard coded plugin, and then the site owner needs to install the update.
So even when Revslider issued it’s inidvidual update, there was no update notification within the site. The site owners never even knew that there is a potential problem. If the developers were lax to issue an update, the exploit that was discovered in this embedded plugin was an open door just waiting to get used.
Make sure you choose a WordPress theme from a reputable source, one that will keep the theme updated properly. In addition, if you have bought a theme and it comes with a limited time update guarantee, understand that you will most likely need to pay up at a later date for an upgrade if one is issued.
What To Do If Your Site Was Hacked
This is a huge article in of itself, but if your WordPress was hacked, it would be wise to know how it was compromised. Obviously there are a few standard procedures to take like regardless of why it happened:
- Deleting all the files in your hosting account for that site and restoring a clean backup
- Changing all the passwords for the WordPress user accounts
- Changing the password for your hosting account
- Checking your hosting account for Cron Jobs that should not be there
- Make sure your file permissions are set correctly
Now all of this won’t matter if your original WordPress was exploited because of an un-updated plugin or theme. So definitely make sure that this is taken care of. If you have a theme that has many features embedded within it, then I would take a look at that developers website for that theme to make sure that no updates have been issued that may not automatically be showing up on your WordPress Dashboard.
I hope that this has helped you understand a bit more about hacked WordPress sites and what you can do about it. If you do have an issue and have a question, I would be glad to help you out, just drop me a line in the comments section below.
- Solving A Google Maps Ranking Drop Puzzle - September 27, 2021
- How To Hide the Address For A Google Business Listing - August 24, 2018
- Having A Bad SEO Month? Take A Look At Search Trends - December 1, 2017
